For many years now, users have turned to Omeka when they feel it is important and necessary to collect materials related to the significant events in the recent past or an ongoing situation that will likely be of historical import. We have always strongly supported these efforts, in part because the original impetus for creating Omeka developed out of our own work at the Roy Rosenzweig Center to collect and preserve the images, stories, and other born digital material related to landmark events in early 21st century.
For us, this work started with the September 11 Digital Archive and the Hurricane Digital Memory Bank. When the September 11 Digital Archive launched, Omeka wasn’t even a glimmer in our eyes, but by 2005 when the hurricanes hit the Gulf Coast, we were well on our way to engineering a platform that would allow users to quickly set up a site for collecting from the public.
The first evidence that people beyond the Rosenzweig Center would look to use Omeka this way came with the tragic shootings at Virginia Tech in April 2007. The April 16 Archive was our first hint that Omeka was going to become part of the infrastructure for archivists, librarians, and public historians who wished to respond to historical events.
At RRCHNM, we have a predisposition to openness. We strive to support open access to historical materials. We build open source software, and we are pleased to see the community make use of that software. Being part of the infrastructure comes with responsibilities for stability and support. Perhaps most important, it comes with a responsibility to respect and protect contributors.
 From its first iteration, the Contribution plugin for Omeka provided administrators with a set of consent options for their participants. They could authorize that their materials be made public with their names, they could be made public but anonymous, or the materials could be contributed and not made public, but be available to authorized persons (using the researcher user permission level). Additionally, administrators could customize the kind of information that they collected from their contributors. For the most part, these options satisfied the use cases we encountered, since anonymity or dark archiving was an option.
From its first iteration, the Contribution plugin for Omeka provided administrators with a set of consent options for their participants. They could authorize that their materials be made public with their names, they could be made public but anonymous, or the materials could be contributed and not made public, but be available to authorized persons (using the researcher user permission level). Additionally, administrators could customize the kind of information that they collected from their contributors. For the most part, these options satisfied the use cases we encountered, since anonymity or dark archiving was an option.
However, the Omeka team, and the cultural heritage community as a whole, has become significantly more concerned about issues of privacy and surveillance. In recent years, libraries, archives, and individual public historians have created collecting sites that use Omeka to gather sensitive materials and gather them from individual who are likely to be vulnerable to surveillance.
-
In the wake of Michael Brown’s shooting in Missouri, Washington University in St. Louis created Documenting Ferguson to collect materials related to the shooting and its aftermath.
-
Then, in April 2015, public historians and archivists came together to create Preserve the Baltimore Uprising to document the events surrounding Freddy Gray’s death and the protests that followed.
-
In the summer of 2015, archivists and community members in Cleveland came together to create A People’s Archive of Police Violence in Cleveland.
Each of these projects work with populations that may be at risk for having their contributions used against them, and there are likely many more similar situations that we do not know about.
Even though the Contribution plugins could be configured to collect very little personal information, they required contributors to provide an email address. Our users have advised us, rightly, that even that level of personal identification could place their contributors at risk. (HT to Documenting the Now, and their thoughtful conversations on these issues.)
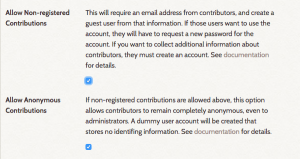 As a result, we have reworked the Contribution suite to allow for fully anonymous contributions. Site administrators who are concerned about protecting their contributors from retaliation and surveillance should upgrade to the most recent version of the plugin (see the Documentation for Contribution v3.1.0). Also, we urge site administrators to carefully craft the terms of service for their sites so that contributors have a very clear understanding of who will have access to their contributions and their personal data.
As a result, we have reworked the Contribution suite to allow for fully anonymous contributions. Site administrators who are concerned about protecting their contributors from retaliation and surveillance should upgrade to the most recent version of the plugin (see the Documentation for Contribution v3.1.0). Also, we urge site administrators to carefully craft the terms of service for their sites so that contributors have a very clear understanding of who will have access to their contributions and their personal data.
Finally, for collected materials that might include personal information that should not be made public, site administrators should consider installing and configuring the Redact Elements plugin. This add-on allows administrators to use regular expressions to redact text (e.g. phone numbers, social security numbers, email addresses) from Omeka metadata elements. While it’s unlikely that projects would collect this information on purpose, contributors might include it in a document or a story. Of course, if an administrator is unsure about the information contained in a contribution, that item can always remain in the repository but not be made public.
We hope that, in combination with clear policies and open communication with contributing communities, these plugins will help site administrators to create and maintain collecting projects that steward their materials and their contributor data responsibly.